Your Cart

Your cart is empty
There are no items in your cart
Keep shopping

Included Software:
Improve your entire music collection, and make every file sound great.
Audio Improvement For Your Music Collection, With One-click.
Add your files to Platinum Notes and it will process them with highest-quality audio filters to improve their volume. Every song will sound like it came from the same mastering engineer.
![]()
Available now for Windows and MacOS
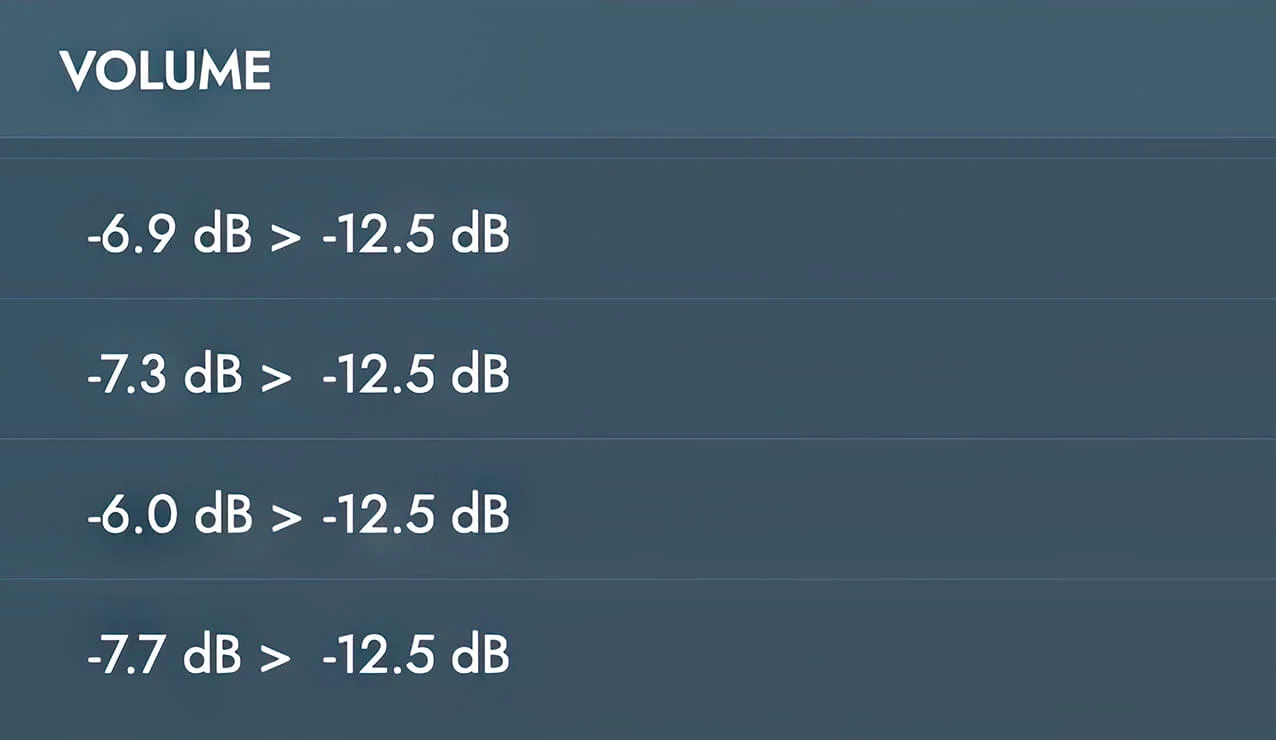
Tracks created by different producers will have different loudness. Platinum Notes standardizes volume across your entire music library. It helps you sound like you have a mastering engineer who takes your DJ sets and applies mastering to them every time you play.
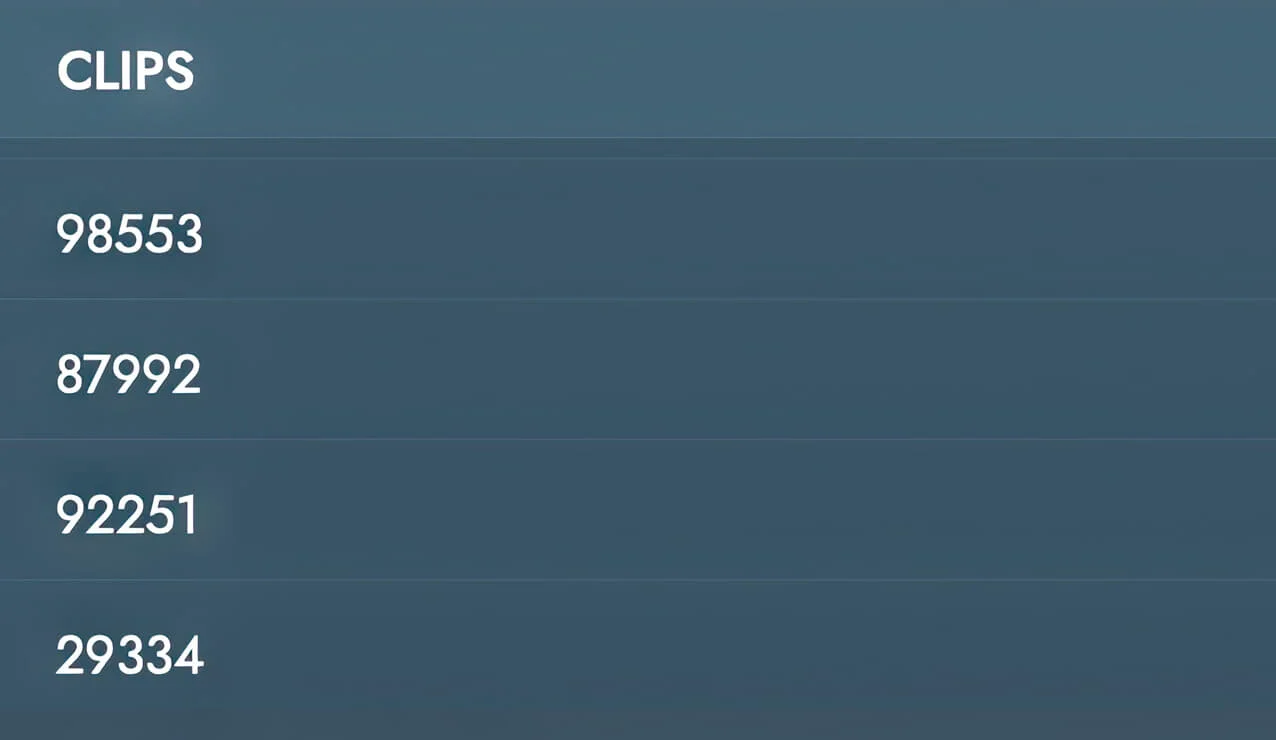
Even high-quality tracks can have imperfections. Platinum Notes fixes clipped peaks and heightens the contrast between quiet and loud sections. 29655.rar
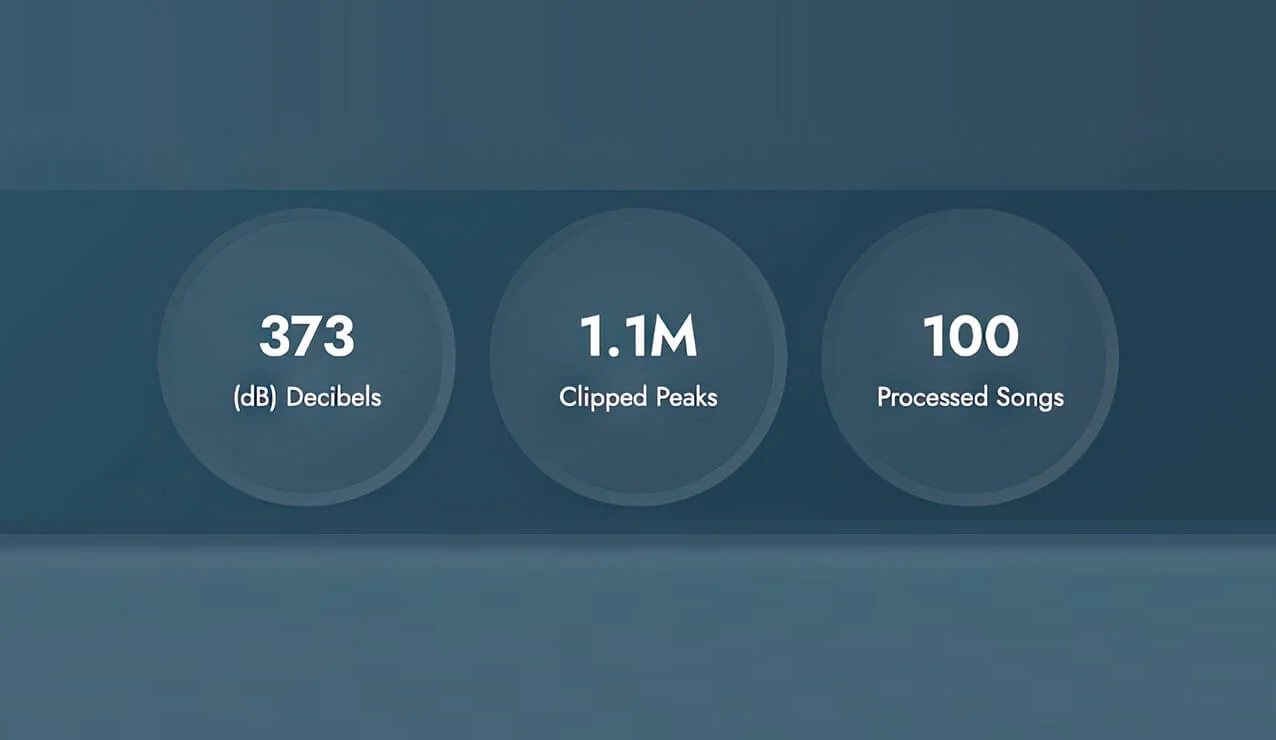
To test it, we took 100 files purchased from Beatport. Platinum Notes fixed 1.1 million clipped peaks, changed 373 decibels of volume, and improved contrast for 100 tracks. People think that Beatport files are perfect, but they came from different labels and different people. The best way to standardize your music library is with Platinum Notes. The archive is designed to look like a


Once you process your music, your other DJ software will sound even better.

The archive is designed to look like a harmless file (such as a PDF or image). When a user double-clicks the file inside the archive, the vulnerability causes WinRAR to execute a hidden malicious script or executable instead of opening the intended document.
Programs designed to exfiltrate browser data, passwords, and cryptocurrency wallets.
Run a full system scan using updated antivirus software (such as Microsoft Defender or Malwarebytes).
Tools that allow attackers to gain full control over the infected machine.
Typically distributed via phishing emails or through malicious links on forums and messaging platforms (e.g., Telegram or Discord). Risk Mitigation & Recommendations
Historically, this file name has been used to deliver various types of malware, including:
The archive is designed to look like a harmless file (such as a PDF or image). When a user double-clicks the file inside the archive, the vulnerability causes WinRAR to execute a hidden malicious script or executable instead of opening the intended document.
Programs designed to exfiltrate browser data, passwords, and cryptocurrency wallets.
Run a full system scan using updated antivirus software (such as Microsoft Defender or Malwarebytes).
Tools that allow attackers to gain full control over the infected machine.
Typically distributed via phishing emails or through malicious links on forums and messaging platforms (e.g., Telegram or Discord). Risk Mitigation & Recommendations
Historically, this file name has been used to deliver various types of malware, including:
Available for Windows and MacOS. Download it and start processing your music right now.